IT Breaches for July 2020
This month, healthcare data breaches keep climbing, Twitter apologizes for its breach and more. Read some of the incidents in the articles below:
CYBERSECURITY NEWS
Social Media, Healthcare and Higher Education struggle in cybersecurity
This month, healthcare data breaches keep climbing, Twitter apologizes for its breach and more. Read some of the incidents in the articles below:
Industry: Social Media
Exploit: Accidental Data Sharing
Twitter sent a notification to business clients last week acknowledging a data breach that exposed the personal and billing information of some users. The breach occurred due to an issue that led to some users’ sensitive information being stored in the browser’s cache. Twitter explained that it recently became aware of this issue. Business users were warned that prior to May 20, 2020, if you viewed your billing information on ads.twitter or analytics.twitter your account’s billing information may be at risk.
Twitter did not release an estimate of the accounts affected, but it did specify that only business customers were at risk, and only a percentage of business customers had any details exposed. The leaked information potentially included email addresses, users’ contact numbers, and the last four digits of credit card numbers used for Ads accounts. Twitter business customers should monitor potentially affected payment accounts.
Industry: Healthcare
Exploit: Internal Email Account Compromise
AMT Healthcare revealed this week that it had experienced a data breach affecting a large pool of customers in December 2019 that was discovered through suspicious activity on an employee email account. The California-based company recently completed an investigation into the incident and contacted those who were affected. Potentially compromised data includes patient names, Social Security numbers, medical record numbers, diagnosis information, health insurance policy information, medical history information, and driver’s license/state identification numbers.
Anyone that may be at risk of compromise was informed this week. Extremely sensitive data was compromised in this breach, and those affected should beware of the potential for fraud, identity theft, and spear phishing attempts that this stolen data creates. A filing of the account posted to the breach portal at the U.S. Department of Health and Human Services noted that potentially affected patients are being offered free credit monitoring services.
When clients choose to do sensitive business with a company, they’re also trusting that company to guard their information. This imperative is even stronger for companies that collect health information. Not only does a data breach cost healthcare organizations patient confidence, but it also costs a fortune in HIPPA-related fines.
Industry: Higher Education
Exploit: Ransomware
The University of California San Francisco (UCSF) confirmed this week that it paid cybercriminals $1.14 million to decrypt data following a ransomware attack. Although UCSF was able to detect the incident quickly, it was not fast enough to allow cybersecurity teams to quarantine the affected servers, and a significant portion of its medical school and research data was encrypted. The ransom was demanded to free essential COVID-19 research data that was captured in an intrusion on June 1. Reports indicate that UCSF was one of four academic institutions targeted in a single week by the Netwalker ransomware group.
Ransomware is a growing menace to every organization, and it’s not just sensitive business or financial data that Dark Web criminals are after. Research data has become an increasingly hot commodity. Paying ransoms to cybercriminals to decrypt research data sets a dangerous precedent. Collecting large sums will embolden other groups that can take down big fish to score big paydays.
New Twist on an Office 365 Phishing Scam
You are probably familiar with the phishing scams that attempt to get you to share your Office 365 password with the criminals, via a fake Office 365 logon page. Well, there is a new twist you need to make everyone aware of in your organization.
PHISHING WITH OFFICE 365 SPOOFS
You are probably familiar with the phishing scams that attempt to get you to share your Office 365 password with the criminals, via a fake Office 365 logon page. Well, there is a new twist you need to make everyone aware of in your organization.
The lure used in this new phishing scam is nothing new; typical social engineering trying to get you to do something you should not do. What is unique is the method used to gain access to your Office 365 organization. Below we explain how the criminals are trying to get access to your information through Office 365.
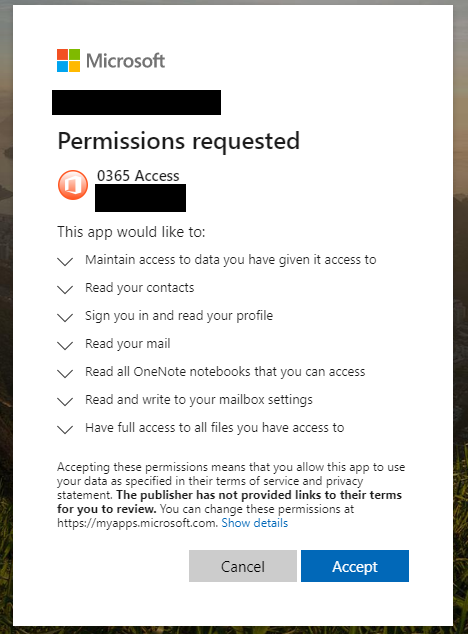
This is the screen you will see when asked to login to Microsoft Office 365.
SPOT A SCAM
Like a lot of these scams, you’ll be presented with a logon page for Office 365 like this one (right), which is the right Microsoft Office 365 logon page, not a fake one:
After you login, or if you were already logged into Office 365 (many people stay logged in), you’ll then see this permissions request pop up (image left). THIS IS THE BAD GUYS asking you to allow them access to everything in Office 365 account!!!
STAY ALERT
Careful attention to the things you are being asked to allow access to should trigger an alarm bell. While this is an actual function in Office 365 that has legitimate uses, if you are casually checking emails and this pops-up, immediately stop what you are doing and alert your cybersecurity team or IT department. This technique abuses the add-ins feature of office 365.
Currently, this phishing exploit appears to be coming in via spoofed sender emails with One Drive attachments. However, there is no reason that the delivery method won’t change to other techniques eventually. The emails are like traditional phishing emails, usually from a spoofed sender. Some email filters will probably catch these before anyone receives them. Security-aware people who know how to spot phishing messages probably won’t fall for this one if they stay alert!