New Twist on an Office 365 Phishing Scam
You are probably familiar with the phishing scams that attempt to get you to share your Office 365 password with the criminals, via a fake Office 365 logon page. Well, there is a new twist you need to make everyone aware of in your organization.
PHISHING WITH OFFICE 365 SPOOFS
You are probably familiar with the phishing scams that attempt to get you to share your Office 365 password with the criminals, via a fake Office 365 logon page. Well, there is a new twist you need to make everyone aware of in your organization.
The lure used in this new phishing scam is nothing new; typical social engineering trying to get you to do something you should not do. What is unique is the method used to gain access to your Office 365 organization. Below we explain how the criminals are trying to get access to your information through Office 365.
This is the screen you will see when asked to login to Microsoft Office 365.
SPOT A SCAM
Like a lot of these scams, you’ll be presented with a logon page for Office 365 like this one (right), which is the right Microsoft Office 365 logon page, not a fake one:
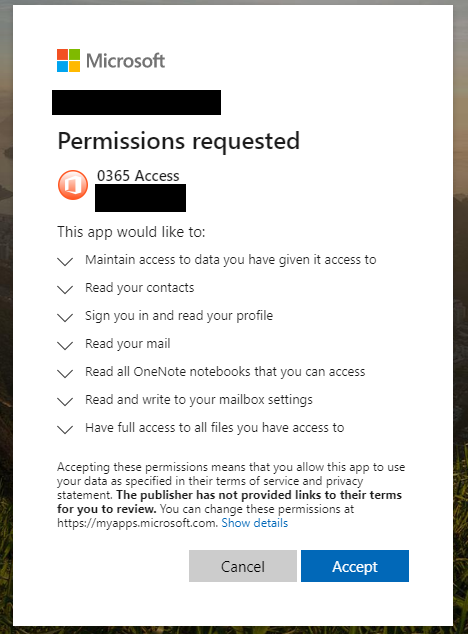
After you login, or if you were already logged into Office 365 (many people stay logged in), you’ll then see this permissions request pop up (image left). THIS IS THE BAD GUYS asking you to allow them access to everything in Office 365 account!!!
STAY ALERT
Careful attention to the things you are being asked to allow access to should trigger an alarm bell. While this is an actual function in Office 365 that has legitimate uses, if you are casually checking emails and this pops-up, immediately stop what you are doing and alert your cybersecurity team or IT department. This technique abuses the add-ins feature of office 365.
Currently, this phishing exploit appears to be coming in via spoofed sender emails with One Drive attachments. However, there is no reason that the delivery method won’t change to other techniques eventually. The emails are like traditional phishing emails, usually from a spoofed sender. Some email filters will probably catch these before anyone receives them. Security-aware people who know how to spot phishing messages probably won’t fall for this one if they stay alert!
4 Lessons From The Most Devastating Cyber Attack In History
Today’s history lesson comes from Wired, who did a really interesting piece last year on the Notpetya cyber attack that targeted the Ukraine, but led to billions of dollars in collateral damage. And really, the story isn't even really about Ukraine or other companies. The story is truly about a nation-state’s weapon of war that was released in such a medium that it knew no borders.
Today’s history lesson comes from Wired, who did a really interesting piece last year on the Notpetya cyber attack that targeted the Ukraine, but led to billions of dollars in collateral damage. And really, the story isn't even really about Ukraine or other companies. The story is truly about a nation-state’s weapon of war that was released in such a medium that it knew no borders. The collateral damage didn’t just affect it’s intended victim, but crossed over everywhere at once. It’s a warning to businesses like yours and mine to be prepared for the worst. You may not be the original intended target, but if you don’t take active precautions then you could easily be taken down like so many other companies and countries mentioned in the following story.
SUMMARY OF NOTPETYA CYBER ATTACK
For four or five years, Ukraine and Russia have been in an undeclared war that has killed more than 10,000 Ukranians. The conflict is so bad that Ukraine has become a testing ground for Russian cyberwar tactics. They have penetrated networks, hacked governmental organizations and companies as well as media outlets to railway firms. They’ve even gone as far as causing widespread power outages.
During this time unbeknownst to anyone, Russian military hackers hijacked Linkos Group company’s update servers to give them a hidden back door into the thousands of PCs around the country and the world. Then they waited…and in June 2017, the Russian saboteurs used the back door they had setup and released a piece of malware called NotPetya, their most vicious cyberweapon yet.
The code that the hackers pushed out was honed to spread automatically, rapidly, and indiscriminately.
“To date, it was simply the fastest-propagating piece of malware we’ve ever seen,” says Craig Williams, director of outreach at Cisco’s Talos division, one of the first security companies to reverse engineer and analyze NotPetya. “By the second you saw it, your data center was already gone.”
Within hours of its first appearance, the worm raced beyond Ukraine and out to countless machines around the world, from hospitals in Pennsylvania to a chocolate factory in Tasmania. It crippled multinational companies including Maersk, pharmaceutical giant Merck, FedEx’s European subsidiary TNT Express, French construction company Saint-Gobain, food producer Mondelēz, and manufacturer Reckitt Benckiser. In each case, it inflicted nine-figure costs. It even spread back to Russia, striking the state oil company Rosneft.
READ THE FULL STORY: https://www.wired.com/story/notpetya-cyberattack-ukraine-russia-code-crashed-the-world/
FOUR LESSONS FOR EVERY BUSINESS FROM NOTPETYA
A number of mistakes, oversights, and criminal acts went into making this attack successful. You’ll also no doubt want to take a look at how something similar might impact you and what steps you can take to protect yourself. There are a lot of takeaways in this story, but here are four very important ones that apply to every business that utilizes computers in running their business:
Enforce utilizing only approved software - Maersk would not have been impacted had ONE finance executive not installed an accounting application on his computer. This stresses the importance of creating and sticking to approved software lists within your organization. Now, this one may have been approved – the story doesn’t say, but in this interconnected world, one mistake can cost a lot.
Patch management of the operating systems and applications - Cyber criminals can infect computers that aren’t patched, and then grab the password from those computers to infect other computers that are patched. Patching was lackluster at best and was a known vulnerability that could have been corrected, but wasn’t.
Backups, backups, backups - Maersk got lucky by finding one domain controller that wasn’t infected as they had no backups – they depended on replicas saving their day, and in this case, I supposed it did, but only because of a power outage isolating one network out of hundreds.
Know your risks and have mitigation plans - Understand that you can do almost everything right and still be impacted – so understand your risks and have mitigation plans for your most critical processes.
Bonus – Vendor risk management. You can do everything right, but if the firms who provide your cloud applications, websites, even IT services are vulnerable, then you must understand that their risks are your risks. Be sure to include these vendors in your overall risk management program and see how they address their risks so you can make informed decisions.
CLOSING
RealTime specializes in helping businesses with complete technology solutions, backups, cyber protections and mitigation plans, vulnerability assessments and more. If you don’t have a plan in place, contact RealTime to begin the process of protecting your business. Feel free to contact us here or call us at (334) 678-1417.
SMB Cybersecurity Checklist (Part 1 of 3)
Given all the news regarding cyberattacks, it’s not hard to get businesses thinking about improving their cybersecurity. But, when those same businesses want to move beyond just thinking about improvement and act to really mature their security, they may feel like they are on their own. After all, the typical small business doesn’t usually have an IT staff, and probably doesn’t know where to begin this journey. Not to worry, we’re here to help.
Given all the news regarding cyberattacks, it’s not hard to get businesses thinking about improving their cybersecurity. But, when those same businesses want to move beyond just thinking about improvement and act to really mature their security, they may feel like they are on their own. After all, the typical small business doesn’t usually have an IT staff, and probably doesn’t know where to begin this journey. Not to worry, we’re here to help.
These are the first 5 things we recommend a small business (really any business) do as they work to improve their cybersecurity posture.
ONE
The very first thing we recommend is to have a plan. If you are not sure how to develop a plan, here is an overview of the different areas you’ll want to review as you begin the process of improving your cybersecurity: https://www.realtime-it.com/blog/solid-cybersecurity-plan.
TWO
You must perform risk and vulnerability assessments for your business. You want to understand (and document) how you use technology in your business and the technical risks you face so you can prioritize your cybersecurity improvement efforts. It is not possible to fix everything at once, and your risk assessment will help you identify what might be addressed easily and what is critical to address immediately.
For the rest of Part 1, we’ll skip ahead a bit in the process to shore up areas every business needs to address if they haven’t already.
THREE
Backups – air-gapped, tested, secured. Simply put, you want to regularly backup all your important data, and have a copy of that backup outside of the building and inaccessible from your local computers. This way, if something bad happens, the backup isn’t affected along with everything else. Don’t forget, you also want to periodically test your backups to make sure the process is working, and the data is up-to-date and usable.
FOUR
Firewall – managed, NextGen security. Your firewall, with the proper security services in force, is one of your primary means of cyber defense. Firewalls have been considered a security necessity for about twenty years now– and no, you can’t get a proper business-grade firewall off the shelf at your local big-box electronics store.
FIVE
Security Awareness Training – ongoing and often. If your staff is using computers and the internet, they need to be aware of the threats, to know what to watch for, and to understand how to report anything out of the ordinary. – We have a great blog on Security Awareness Training here with a lot of great links.
Finally, even though we said we’d only discuss the first five steps to consider in addressing stronger cybersecurity, we really want to make sure you understand how important it is for you to obtain adequate cyber insurance appropriate to your business type and cyber risks. Talk to your insurance agent and ask for qualified resources and options to help you find the best policy to meet your needs.
ARE YOU A SMALL BUSINESS LOOKING TO BUILD REVENUE?
For a small business owner like you, building and supporting a baseline IT infrastructure that provides reliable 24/7 services to you and your customers can be forbiddingly expensive. Even a wobbly, poorly supported infrastructure can be a budget breaker.
LET’S BUILD SOME REVENUE USING THE CLOUD…
Do you want to save money and direct your time and energy into boosting profits? We suggest updating your infrastructure to include the cloud.
For a small business owner like you, building and supporting a baseline IT infrastructure that provides reliable 24/7 services to you and your customers can be forbiddingly expensive. Even a wobbly, poorly supported infrastructure can be a budget breaker.
REALTIME CLOUD HOSTING is a great way to eliminate a lot of headaches for your business.
Large capital expenditures, high fixed-labor costs, and endless spending for upgrades don’t have to be your fate. The cloud offers a way out it can not only save you money, it eliminates a lot of headaches and can spur growth and boost profits. Let’s look at just a few things the cloud can do for you.
Capex: Most of the expenses of hardware disappear into the cloud. Servers, cabling, all the redundant equipment needed for backup can be handled by a cloud Service provider.
And more importantly, if you need to ramp up quick for an unexpected surge in business, a cloud service provider can easily accommodate your demands as needed.
Disaster recovery is simplified: While you always need disaster recovery plans, the biggest head- aches disappear. When you handle everything in-house, considerable expenditures arise if you want high reliability. Redundant equipment, fully loaded with software is required in case of hardware failure. Uninterruptible power supplies to support the full load of all your servers and backups can be extraordinarily expensive. And even if you keep a lot of your infrastructure on-site, the cloud can be used as a reliable data backup system
Labor: The cloud can cut and/or re-allocate your IT labor costs. The benefits of the cloud in the area of IT resources are twofold.
First, you eliminate the need for 24/7 resources to support your infrastructure. Even if you have only minimal in-house support, emergency on-call break/fix services come at very high hourly rates, and cannot always respond fast enough to eliminate downtime. Of course, your cloud fees include the labor needed to support your infrastructure, but you are sharing that labor cost with all the other renters. Economies of scale really step in when it comes to labor, and this is a condition a small business can’t create on its own.
Second, when you migrate to the cloud, your in-house IT resources can be re-directed to strategic IT planning for future growth and boost profit. This staff can now be used for innovation, not just housekeeping.
And finally, the cloud isn't blue- It's green. While big server farms use enormous amounts of energy, they are a more efficient method than equipment dispersed in offices worldwide.
Other unexpected benefits: As you move your IT into the cloud, some unseen expenses go away. The extra office space that houses equipment no longer needs to be leased, or can be used to house other revenue producing resources, like a few new salespeople. The electric power to drive it all doesn’t come free, and the cooling power to keep everything from overheating is often an overlooked cost of in-house infrastructure.
5 FOUNDATIONS OF A SOLID CYBERSECURITY PLAN
Do you know the five steps to create a solid cybersecurity plan? Continue reading to find out what steps to take and other resources for your business.
5 FOUNDATIONS OF A SOLID CYBERSECURITY PLAN
Identify - Define your business assets and what you need to protect.
Protect - Operate securely and actively protect your valuable information.
Detect - Observe and alert on bad behaviors and other indicators of compromise.
Response - Guide your actions with your response plans.
Recovery - A safety net is imperative for a solid Continuity and Disaster Recovery Plan.
CRAFTING A SOLID CYBERSECURITY PROCESS
The first steps in crafting a solid cybersecurity process for your business fall under the IDENTIFY domain: perform a Risk Assessment, a Vulnerability Assessment, and an Impact Analysis on your business to help document your business risks.
Let’s dig into this a bit. Beware, lots of links ahead!
Here is a great resource that you’ve already paid for with your tax dollars – the NIST Small Business Cybersecurity corner, https://www.nist.gov/itl/smallbusinesscyber. NIST has a roadmap, https://www.us-cert.gov/sites/default/files/c3vp/smb/DHS-SMB-Road-Map.pdf to help visualize the journey to improved cybersecurity for your business. This guide covers the five foundations discussed earlier in a user-friendly format -https://nvlpubs.nist.gov/nistpubs/ir/2016/NIST.IR.7621r1.pdf.
Risk Assessment – compare proven best practices against how your business approaches various actions/processes that can impact your security. RealTime has a shortened Risk Assessment to get you started, all based upon the NIST Cybersecurity framework. Save some time by calling us to review your processes or use the full assessment using the NIST framework tools provided below:
Latest NIST CSF Framework PDF, version 1.1 https://nvlpubs.nist.gov/nistpubs/CSWP/NIST.CSWP.04162018.pdf
Spreadsheet to perform the evaluation with https://www.nist.gov/document/2018-04-16frameworkv11core1xlsx
Vulnerability Assessment – Test your network inside and out for technical holes using this assessment. A competent professional should perform this step and RealTime is available. You can do this yourself, but it’ll be faster, cheaper, and better to engage a professional to perform this step.
Business Impact Analysis – Outline the most important things your business does and technologies or systems used to perform these important functions. This will help you focus your resources where you can get the most positive impact to your business. A Business Impact Analysis is definitely a DIY step – no one knows your business better than you. RealTime can help guide the process and the risk discussion if you need it.
IDENTIFIED RISKS AND POTENTIAL IMPACTS
After you’ve gathered this information, prioritize your findings to help make educated decisions on
What risks you need to mitigate now;
What risks to plan to address in the future;
What risks you choose to accept for now.
The goal is for your business to understand what your identified risks are and the potential impacts; this allows you to prioritize and begin mitigating those risks. Most small businesses find that many risks are process/procedure oriented. These things can largely be addressed internally with proper staff training on new processes.
Additionally, it is likely that there will also be technical risks and these will need to be addressed by your Technology Department or an outsourced provider like RealTime.
ARE YOU GOING TO SLEEP WELL TONIGHT?
We hope this piqueS your interest in getting on the path to improving cybersecurity for your business. EVERY business, small or large, needs a comprehensive cybersecurity program now more than ever. Call us if we can help or fill-out the form below, (334) 678-1417.
Pro tip – this is part of RESPOND, but is something you’ll want to have in place sooner rather than later – Cyber liability insurance. Talk to a qualified insurer, ask lots of questions and make sure the policy is going to be effective in providing the coverage your business needs.
[Guest post written by RealTime VP Todd Swartzman]
WANT ADDITIONAL RESOURCES?
We have resources such as a Business Impact Analysis spreadsheet and other items to help your business. Just fill-out the form below and we will help you out.